According to a report published by the London-based think tank British American Security Information Council (Basic), the UK Trident submarine fleet is vulnerable to cyber-attacks.
According to the report “Hacking UK Trident, A Growing Threat,” a cyber attack against a submarine could have ‘catastrophic’ consequences, including loss of life.
“A successful attack could neutralise operations, lead to loss of life, defeat or perhaps even the catastrophic exchange of nuclear warheads (directly or indirectly).” reads the report. “But the very possibility of cyber-attack and the growing capability to launch them against SSBNs, could have a severe impact upon the confidence of maintaining an assured second-strike capability and therefore on strategic stability between states”
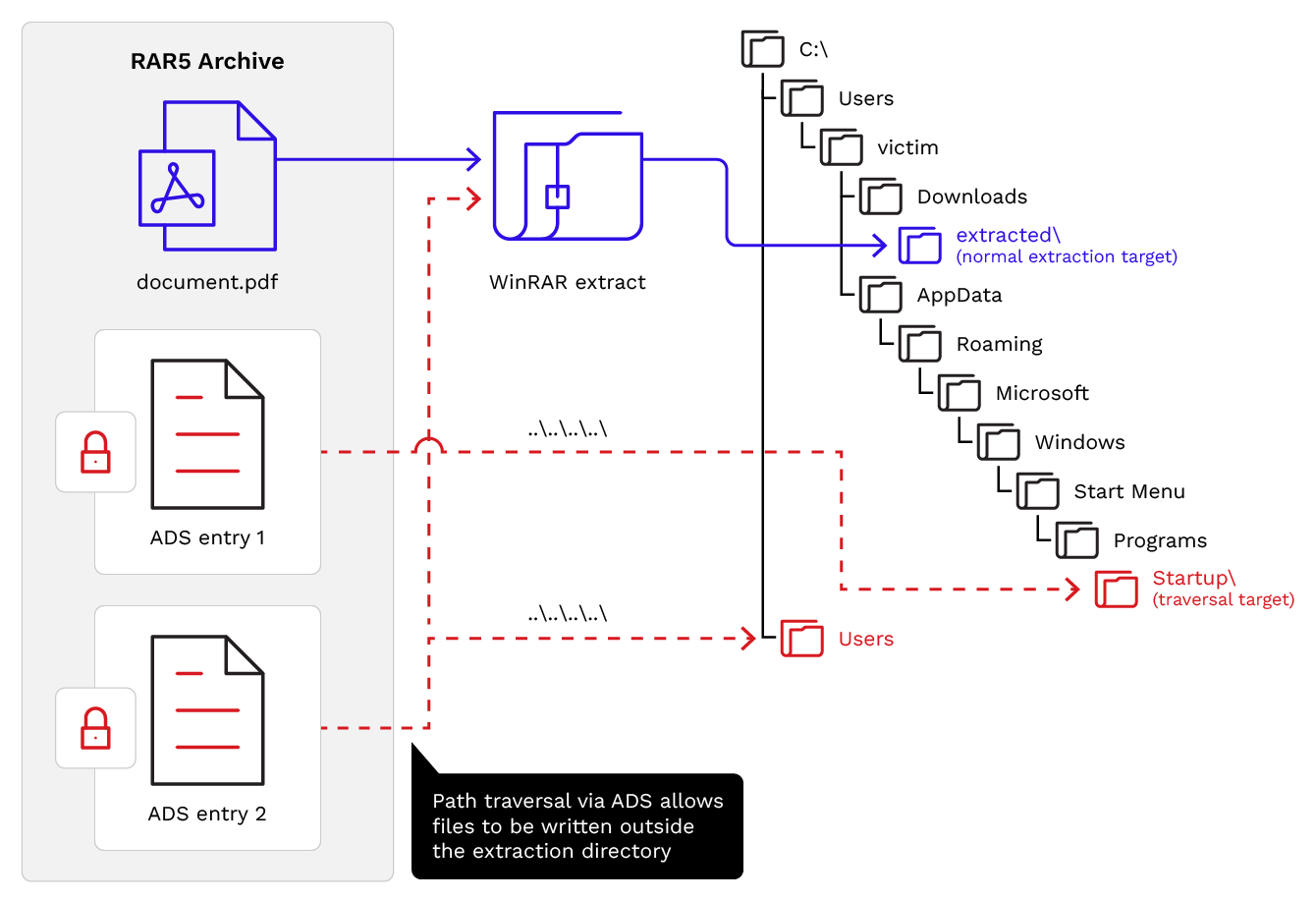
Military officials consider Trident submarines safe from hacking because they leverage air-gapped networks, but authors of the report expressed skepticism.
The researchers believe that vessels are not vulnerable to cyber attacks during normal operations while are in the sea, but they could be targeted with a malware-based attack at other points, such as during maintenance while docked at a naval base.
Trident submarines use same Windows software deployed at the NHS that were recently destroyed by the WannaCry attack.