
The last couple of years has been characterized by the raise of state-sponsored cyber attacks, governments have increased cyber capabilities to defend their critical infrastructures from offensive originated in the cyberspace but they also improved tactics to offend and spy on foreign government networks.
Governments and private business of countries such as US, Japan and UK have been constantly hit by cyber attacks for sabotage or cyber espionage, for this reason the US Department of Justice has decided to take the field persecuting criminals.
Destroying an American computer system or stealing data from a defense contractor may be considered an offense and therefore punishable by law enforcement despite it set in the cyber space.
To date the responsibility to prevent and respond to cyber attacks was assigned to dedicated groups within DoD, Department of Homeland Security or National Security Agency.
The Justice Department has recently started a multifaceted initiative under its division named NSCS (National Security Cyber Specialist) training more than 100 prosecutors that will be used as support for various agencies such as NSA.
John Carlin, the principal deputy assistant Attorney General in Justice’s national security division said:
“NSA, we have some oversight function on them but they are our client when we go in front of the foreign intelligence surveillance court,” .
Similar discussion for FBI, the DOJ has as target the identification of the most interesting cases that can finally can take legal action, once identified it desires to drive the effort of the investigation of the Bureau.
The DoJ desires to declare war to hackers, also if they operate for foreign governments, the principle is the same followed for spies, Carlin declared that the DOJ could persecute people working for foreign governments. High officials of foreign governments that arrange and coordinate cyber attacks against US networks can be persecuted like any other criminal, despite that doesn’t mean there’s an expectation that he’ll ever be brought to court. Carlin reiterated that similar procedure have been already applied, in 2011 an Iranian Al Qods official was charged with conspiring to kill Saudi Arabia’s ambassador to the U.S.
If the indictments could be not very effective from the point of view of hackers persecution it is fundamental in all those cases in which intellectual properties are stolen from companies and used for the production of products with high technological content, it is the case of a private company that uses stolen technology and due this reason it could be charged.
“Whether it is a state-owned enterprise or a state-supported enterprise in China — if you can figure out and prove that they’ve committed the crime, charging the company means they can’t do business in the U.S., or in Europe,” “It affects their reputation and that then causes them to recalculate: ‘Hey, is this worth it?’” Carlin said
Recently the Defense Security Services published a report “Target US Technologies 2012” that proposes an analysis of foreign attempts to obtain illegal of unauthorized access to sensitive or classified information and technology resident in the US.
“DSS mission is to support national security and the warfighter, to secure the nation’s technological base, and oversees”
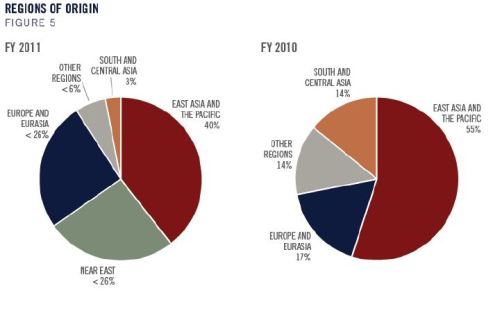
The East Asia and The Pacific accounted for 43% of total, the Near East for 18%, Europe and Eurasia for 13% and South and Central Asia for remaining, the alarming data is related to the increase of number of reports received from industry that is around 75% more respect previous year (2010).
Another concerning factor is related the expansion of the degree of interaction between collectors despite their different origin.
The order of the regions linked to the most prolific collectors of U.S. information and technology remained unchanged from fiscal year 2010 (FY10), commercial remained the most common collector affiliation and the top four most targeted technology categories remained the same (information systems (IS), lasers/optics/sensors (LO&S), aeronautics systems, and electronics).

“In FY11, suspicious network activity (SNA) was the most prevalent collection MO for entities originating from East Asia and the Pacific; SNA figured no more prominently than fifth in any other region. Due to the nature of SNA, it remains difficult to attribute such collection attempts to an entity or even to a region of origin.”
The data proposed give an idea of the amplitude of the phenomena, from a technological point of view it’s hard to defend sensitive information from constant attack of foreign governments that’s why The Justice Department is thinking to “persecution” and “indictment”, the unique ways to mitigate risk of theft of intellectual property.
Companies that steal technological knowledge shall be charged and be penalized in the possibility of sale of their products and services. I believe, however, that this approach does not lead to a complete solution of the phenomenon of cyber espionage, consider the fact that most times intellectual property stolen is used for the internal market of the nations who commit the crime, as it is also confirmed by the most affected sectors . Generally the theft of information in areas such as defense and military is used to bridge the technological gap towards technologically advanced countries.
The initiative of the DOJ is a first step but certainly not resolutive.
Pierluigi Paganini