
The Russian APT group known as Turla (also known as Waterbug, KRYPTON and Venomous Bear) has continued to improve its Carbon backdoor, experts from ESET detected new versions released on a regular basis.
Carbon is a second-stage backdoor that is used after an initial reconnaissance phase of an attack, it involves malware such as Tavdig.
The Turla’s arsenal is composed of sophisticated hacking tools and malware tracked as Turla (Snake and Uroburos rootkit), Epic Turla (Wipbot and Tavdig) and Gloog Turla. In June 2016, researchers from Kaspersky reported that the Turla APT had started using Icedcoffee, a JavaScript payload delivered via macro-enabled Office documents.
Last time the researchers reported Turla‘s activities was February 2017, when experts at Kaspersky Lab have discovered a new piece of JavaScript malware linked to the group targeting organizations in Greece, Qatar, and Romania.
Turla has been active since at least 2007, the hackers launched several high-profile attacks against targets worldwide, including the ones aimed at Swiss defense firm RUAG and the U.S. Central Command.
Carbon, aka Pfinet, is once of the tool in the arsenal of the hacking crew, researchers from ESET described it as a lite version of Uroburos.
Carbon is a second-stage backdoor that is typically deployed after the reconnaissance phase of an attack, it has several components, including a dropper, a command and control (C&C) communications element, an orchestrator, and a loader that executes the orchestrator.
The orchestrator is used to inject the C&C communications library into a legitimate process, and dispatch the tasks received via the C&C library to other bots that are located on the network.
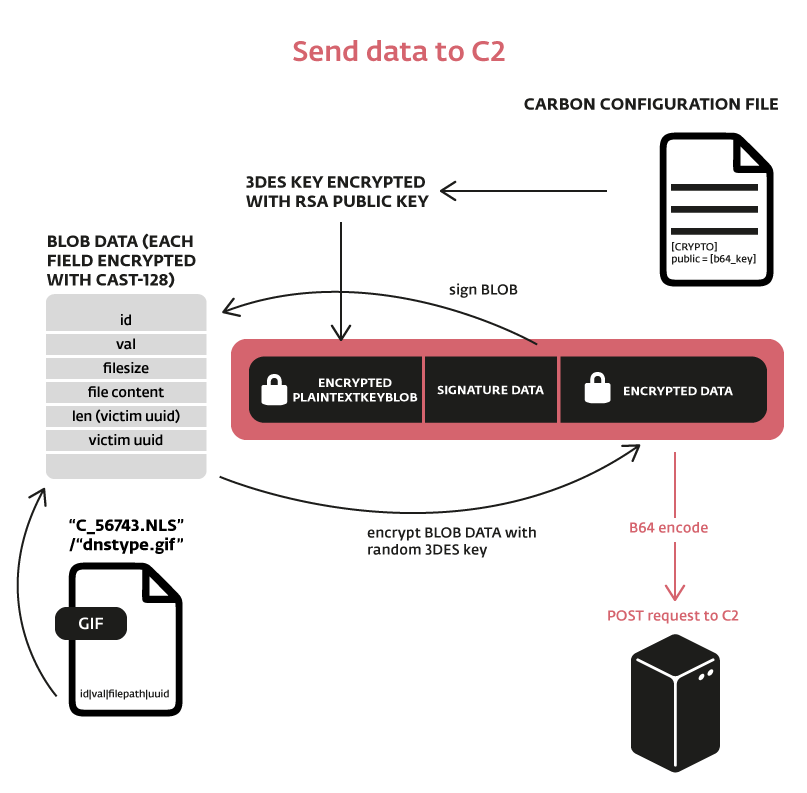
ESET has identified several versions of Carbon compiled last year; the most recent one was compilated on October 21, 2016. The newer versions of the Carbon malware make a massive use of encryption.
Almost any component is a DLL file, except for the loader, which is an EXE file.
“The Turla group is known to be painstaking and work in stages, first doing reconnaissance on their victims’ systems before deploying their most sophisticated tools such as Carbon.
A classic Carbon compromise chain starts with a user receiving a spearphishing email or visiting a previously compromised website, typically one that the user visits regularly — a technique known as a watering hole attack.” reads the analysis shared by ESET.
“After a successful attack, a first stage backdoor — such as Tavdig or Skipper — is installed on the user machine. Once the reconnaissance phase is over, a second stage backdoor, like Carbon, is installed on key systems.”
Threat actor behind Turla have modified their tools everytime they were detected in the wild. Researchers observed that in the case of Carbon, the hackers changed file names and mutexes in the version 3.8 released in the summer of 2016.
Experts noticed that before the malware start communicating with C&C, it checks the infected system for the presence of packet capture software, such as Wireshark and Tcpdump.
“Before communicating with the C&C server or with other computers, the malware ensures that none of the most common packet capture software is running on the system:
Stay Tuned …
[adrotate banner=”9″]
(Security Affairs – Turla APT group, cyber espionage)
[adrotate banner=”13″]