
It’s arrived, the Raspberry Pi Foundation has presented a new Raspberry Pi model the Raspberry Pi 3 Model B.The Raspberry Pi 3 Model B in the successor of the Raspberry Pi 2 introduced exactly one year ago and comes after the presentation of a $5 Raspberry Pi Zero.
The Raspberry Pi is a tiny computer that developed in England, it is versatile and its characteristics make it suitable for adoption in many projects.Raspberry Pi series is very cheap, it has been estimated that more than 8 Million units have been already sold.
“In celebration of our fourth birthday, we thought it would be fun to release something new. Accordingly, Raspberry Pi 3 is now on sale for $35 (the same price as the existing Raspberry Pi 2)” wrote Eben Upton, CEO of Raspberry Pi.

The new Raspberry Pi 3 has a new heart, previous versions were based on a 32-bit architecture with a 900MHz quad-core ARM Cortex A7, meanwhile the new model is based on a 64-bit processor, with quad-core 1.2 GHz ARM Cortex-A53 CPU.
The new Raspberry Pi 3 Model B has built-in Wi-Fi (802.11n) and Bluetooth 4.1 connectivity, meanwhile previous models needed USB adapters to add these functionalities.
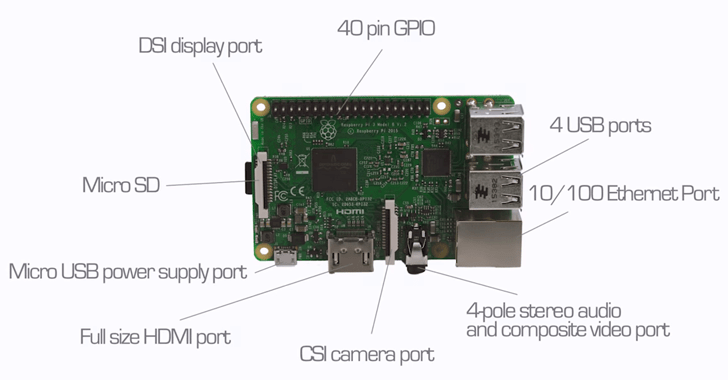
The new version of the Pi comes with four USB ports and according to its creators the new model reached 50-60% increase in performance thanks to a series of improvements.
“Combining a 33% increase in clock speed with various architectural enhancements, this provides a 50-60% increase in performance in 32-bit mode versus Raspberry Pi 2, or roughly a factor of ten over the original Raspberry Pi.” continues Upton.
Another novelty of the Raspberry Pi 3 is the compliance with Windows 10 IoT obtained thanks to a collaboration between the Raspberry Pi Foundation and Microsoft.
Below the technical details of the new Raspberry Pi 3:
(Security Affairs – Microsoft Enhanced Mitigation Experience Toolkit, Hacking)