The security expert David Longenecker discovered that ASUS Wireless Routers RT Series are vulnerable to Man-in-the-Middle attacks. The researcher explained that that the routers download updates via HTTP without an encryption protocols as explained in the blog post by Longenecker. An attacker could exploit the security issue to compromise the device, because the updates are not provided over a secure channel (i.e. Through HTTPS using the Transport Layer Security (TLS) protocol).
“Today I am disclosing one additional vulnerability, submitted as CVE-2014-2718. The ASUS RT- series of routers rely on an easily manipulated process to determine if an update is needed, and to retrieve the necessary update file. In short, the router downloads via clear-text a file from http://dlcdnet.asus.com, parses it to determine the latest firmware version, then downloads (again in the clear) a binary file matching that version number from the same web site.” explained Longenecker in the blog post.
“The ASUS RT- series of routers rely on an easily manipulated process to determine if an update is needed, and to retrieve the necessary update file,” “Since the router downloads via HTTP instead of HTTPS, there is no way to validate that the server at the other end is in fact the ASUS server and not an impostor.”
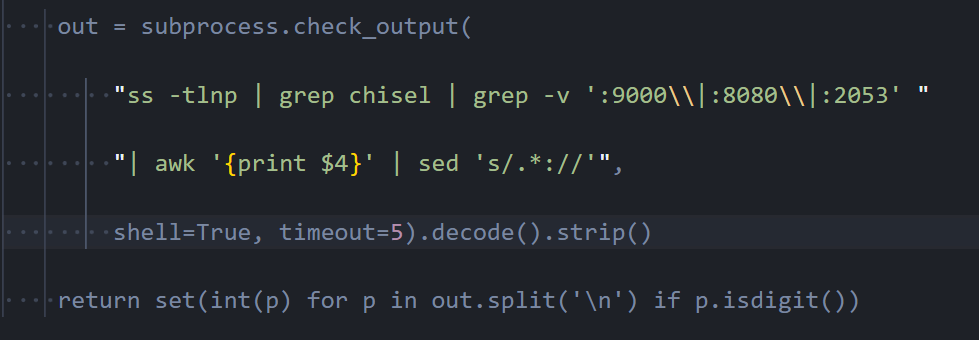
According to the expert, the updating process for the ASUS Wireless Routers RT Series is insecure. The network device first downloads a clear-text file list containing the latest firmware builds, then it parses the downloaded file searching for a newer available firmware update. Once a new firmware update is available, the router downloads the firmware package.
“Knowing the actual latest revision for one or more target router models, we can increment the extended version (EXT####) and place the file in a matching path (pub/ASUS/LiveUpdate/Release/Wireless/wlan_update_v2.zip) on a server that we control. ” wrote Longenecker.
The process is clearly exposed to external attack like the Man-in-the-Middle, this means that an attacker can tamper with both the list and software and compromise the router to access/manipulate the traffic that passes through it.
The ASUS Wireless Routers RT Series affected by the issue are: RT-AC68U, RT-AC68U, RT-AC66R, RT-AC66U, RT-AC56R, RT-AC56U, RT-N66R, RT-N66U, RT-N56R and RT-N56U.
Experts speculated that also other ASUS Wireless Routers RT Series are affected by the same issue: RT-N53, RT-N14U, RT-N16 and RT-N16R.
ASUS quickly issued an undocumented fix to solve the problem, it is necessary that users will download it directly from the official ASUS website (asus.com), avoiding to use the built in update feature implemented in the router GUI.
Security Affairs – (ASUS Wireless Routers RT Series, hacking)