
Most of the major banks and companies that suffer this type of attacks make people aware of phishing, but despite the high level of awareness of the threat, the phenomenon does not slow down, indeed seems to accelerate more and more. Run a phishing campaign is becoming quite easy also for inexperienced criminal that wants to steal user data. As a direct consequence, criminals with the necessary technical knowledge started to offer phishing kits that can be downloaded by anyone for few dollars as explained by Symantec:
“Scammers can buy these kits for between US$2 to $10, though they have also been observed stealing them. They don’t have to have a lot of technical skills to use these kits—with just a little knowledge of PHP, they can customize their phishing pages to suit their needs. The scammers can then use the stolen data for their own purposes or sell it on underground marketplaces. ” states Symantec.
Among the most versatile phishing kit identified by the Anti – Fraud Command Center ( AFCC ) RSA, there was the Universal phishing kit. This phishing kit was easily configurable and very versatile.
Many other phishing kits are now available on the web, some of them for free, most of the buyers usually ignore that sometimes the sellers hide part of the code in the kits pages. The hidden code could allow them to siphon data collected from victims unbeknownst to the criminals that use phishing kit … basically, the scammer is scammed.
The procedure
Once users downloads the phishing kit need to make the right steps in order to go live. First of all, they have to find a website to host the phishing page. Crooks use numerous tools available on the market to scan the internet and search for a vulnerable website to control. Typically scammers use compromised servers or they rent an entire infrastructure to run the malicious campaigns.
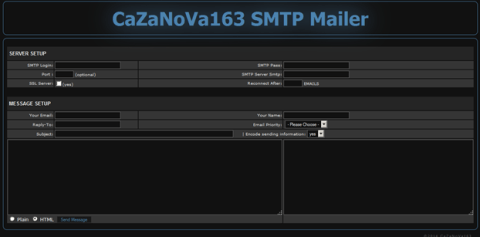
Once scammers have found the suitable place to locate the phishing page they can upload them to start the scam. Once the phishing kit was deployed, phishers need to install a Simple Mail Transfer Protocol (SMTP) mailer so that they can import a list of users’ emails and send the phishing messages in bulk.
In order to remain under the radar, criminals adopt different techniques to hide phishing kits to search engines and security firms, some of the tactics, as explained by Symantec, include:
The data collected could be used by the scammer or sold in the numerous underground markets hosted on the Deep Web. Here you can buy stolen credit card data in some cases, sellers also offers replacement services in case of deactivation of the card, for an extra few Bitcoins.
Other phishing tools:
In addition to the phishing kits, the underground offer for scammers includes video tutorials that explain how to create phishing pages, or build your own page with tools of social engineering included in the principal Linux distributions for Pen Tester. Every novice could be a dangerous scammer, for this reason a wider audience of criminals is attracted by this profitable business.
Whichever way the phishing page is created to avoid being scammed it is always best to check that you are using an https connection before entering your personal data. Unfortunately, this precaution is not enough to protect users, it is important to verify that the site belongs to the company that you are dealing with, especially verifying the field Issued to in the certificate when you are using the HTTPs protocol.
The experts are observing the adoption of HTTPS for mobile phishing. As explained by Paul Pajares, Fraud Analyst at TrendMicro, use HTTPS for phishing activities, doesn’t need a supplementary effort for cyber criminals, they can either compromise sites that already use HTTPS, or use legitimate websites that already use HTTPS.
“One of the reasons for this spike is that it is easy for cybercriminals to create websites that use HTTPS: they can either compromise sites that already use HTTPS, or use legitimate hosting sites or other services that already use HTTPS. There is no need for the cybercriminals to acquire their own SSL certificate, since they have just abused or compromised servers that do have valid certificates.” reports the blog post published by TrendMicro.
Written by Alessandro Contini
Alessandro Contini operates as Cyber Security Consultant in national and international realities. Starting from a long experience and technical expertise on system architectures in particular related to Critical Infrastructure. Alessandro collaborates as Cyber Intelligence specialist to find deeper information in Cyber Crime and Terrorism scenarios.
with Pierluigi Paganini
(Security Affairs – Phishing kits, cybercrime)