
Researchers from Kroll’s Cyber Threat Intelligence team discovered a malicious Python package uploaded to the Python Package Index (PyPI) that contained a fully-featured information stealer and remote access trojan tracked as Colour-Blind.
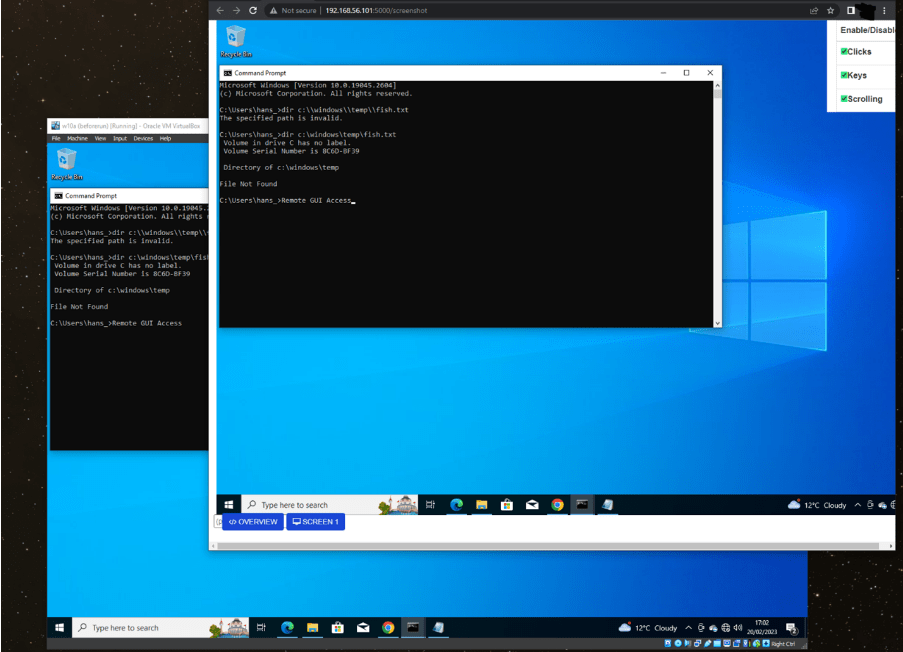
Below is the list of capabilities supported by the RAT through the control interface includes:
The malicious package is named colourfool. The experts pointed out that the Colour-Blind malware “points to the democratization of cybercrime” allowing threat actors to develop their own variants based on the shared source code.
The package contained a single Python file of note, which is a large “setup.py” that was modified four days before its discovery. The script was developed to download a file from a remote server, then silently execute it.
The experts noticed something suspicious in the function that provided the URL for downloading the malware.
“It attempted to get a URL from a pastebin[.]com snippet and failing this returned a hardcoded discord content delivery network URL. Within a legitimate library, the use of hardcoded URLs for downloading executable resources “on the fly” is uncommon.” reads the report published by Kroll. “This is particularly true when those URLs aren’t persistent and unlikely to be reachable after a short period of time.”
The second stage archive contained only one file “code.py” which is over 300 kilobytes (KB) in size.
This second script includes multiple modules that allows the malware to conduct malicious activity such as keylogging, stealing cookies, and disabling security products.
The malware performs some checks to avoid being executed in a sandbox, but it has a light obfuscation. The malware maintains persistence by adding a Visual Basic (VB) script named “Essentials.vbs” to the “Start Up” folder within the user’s “Start Menu.”
The malware relies on the anonymous file transfer service“transfer[.]sh,” to exfiltrate stolen data.
“The malware triggers multiple subprocesses, including threads for cookies, passwords and cryptocurrency wallet theft.” continues the report. “As a method of remote control, the malware starts a Flask web application, which it makes accessible to the internet via Cloudflare’s reverse tunnel utility “cloudflared,” bypassing any inbound firewall rules.”
Kroll highlights that the interesting features supported by Colour-Blind malware can easily be written in modern languages such as Python.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Colour-Blind)