Zeus Trojan is becoming even more complex, its evolution is unpredictable due to the intense activity in the underground on its source code. Various forums in the underground offer customization service to adapt the behavior of Zeus trojan to the new fraud scheme. Last version of the popular Banking Trojan detected by the Trusteer security firm is not only able to steal funds from its victims but it also tries to recruit them as ‘Mules’
Security firm Trusteer revealed that a group of criminals using the popular Zeus banking Trojan has started a recruiting campaign displaying ads for job scams once victim visits a popular job site, CareerBuilder [dot] com.
The investigation conducted by Trusteer focused also on employment websites that have long been a target for cybercriminals searching for the user’s credentials through malware distribution and mule recruitment.
The Zeus Trojan found by Trusteer uses HTML injection to advertise a mule recruitment site when a victim visits CareerBuilder [dot] com. Mules are an essential component of the scam life cycle, in particular for cash-out money, in the past recruiting web site were used by criminal organizations to recruit these figures.
“Money mules are always a scarce resource and whenever criminals do recruit them, they keep a pretty good eye on them,” he said. “At the end of the day, you really can’t cash out unless you have a mule.” Commented Etay Maor, fraud prevention solution manager with Trusteer.
Typically the criminals create a job opening for “financial managers” with possibility to earn working at home, in reality those people that respond to the announcement serve as the money laundering component for cybercrime gang. Principal employment websites are aware of this illegal practice and have created dedicated security team including anti-fraud competences. The web site used for mule recruitment is marketandtarget [dot]com as reported in the Zeus Trojan configuration file, site that is currently down.
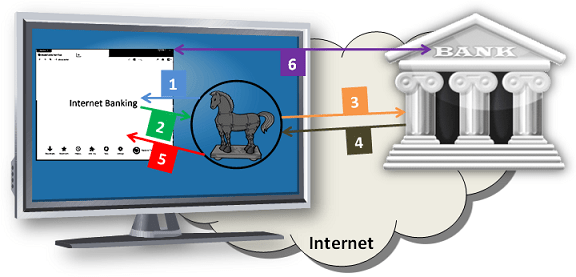
On the other side malware authors have refined their techniques to avoid controls operated by site managers, the last variant of The Zeus Trojan in fact implements a Man-in-the-Browser (MitB) techniques to present the victim with an advertisement for a mule recruitment site every time he visits CareerBuilder [dot] com.
Man-in-the-Browser malware are commonly used by cybercrime to steal data from victims or to redirect them to compromised web sites such as the specific case we are analyzing.
The variant of Zeus trojan using HTML inject adds data fields or to present bogus messages to redirect the victim to a fake job offering while he is visiting legitimate employment site CareerBuilder [dot] com, in this way the victim plays redirection as a legitimate operation of the access to a job opportunity.
The availability of the source of Zeus Trojan on the black market potentially opens to an infinite number of possibilities that we will meet in the near future and represents a success for the industry of malicious software.
| [adrotate banner=”9″] | [adrotate banner=”12″] |
(Security Affairs – Zeus Trojan, cybercrime)
[adrotate banner=”5″]
[adrotate banner=”13″]