
Do you remember the BASHLITE malware? It was a strain of malware (also known as Lizkebab, Torlus and Gafgyt) detected by experts at Trend Micro shortly after the public disclosure of the ShellShock bug.
The BASHLITE malware includes the code of the ShellShock exploit and it had been used by threat actors in the wild to run distributed denial-of-service (DDoS) attacks.
It could infect multiple Linux architectures, for this reason, crooks used it to target Internet of Things devices.
In June, experts from the security firm Sucuri spotted a botnet composed of tens of thousands of CCTV devices that had been used by crooks to launch DDoS attacks against websites.
The BASHLITE source code was leaked online in early 2015, malware developers used it to create their own variant.
Now experts from Level 3 and Flashpoint confirmed the overall number of devices infected by the BASHLITE malware is more than 1 million.
The number includes compromised devices belonging to several botnets, according to the experts, almost every infected device are digital video recorders (DVRs) or cameras (95%), the remaining is composed of routers (4%), and Linux servers (1%).
“Of the identifiable devices participating in these botnets, almost 96 percent were IoT devices (of which 95 percent were cameras and DVRs), roughly 4 percent were home routers and less than 1 percent were compromised Linux servers. This represents a drastic shift in the composition of botnets compared to the compromised server- and home router-based DDoS botnets we’ve seen in the past.” states a blog post published by Level 3 firm.
The researchers have been tracking more than 200 C&C worldwide used by the BASHLITE botnets. Fortunately, the IP addresses of the C&C servers was found hardcoded in the instance of malware detected in the wild making easy for experts to shut down them.
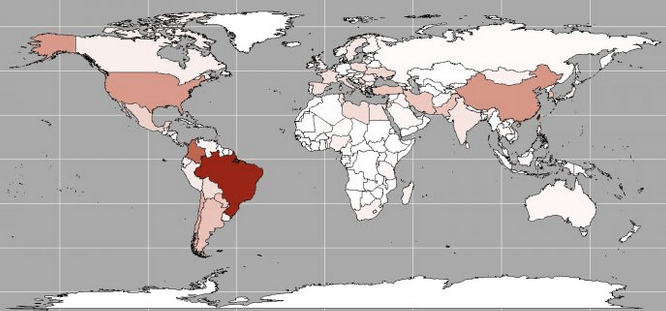
The researchers provided interesting details about the Global Distribution of the gafgyt Bots, the vast majority of infected devices are located in Brazil, Taiwan and Colombia.
“Of the bots we’ve observed participating in attacks, peaking at more than 1 million devices, a large percentage are located in Taiwan, Brazil and Colombia. A large majority of these bots were using white-labeled DVRs generically described as “H.264 DVRs” and DVRs manufactured by the company Dahua Technology.” continues the post. “We have contacted Dahua Technology to make them aware of this issue. Our investigation shows more than one million of these two types of devices are accessible on the internet, providing a large pool of potential bots.”
It is quite easy for hackers to compromise DVRs that are affected by multiple critical vulnerabilities. In many cases, the same flawed software is used by multiple vendors for their devices.
“Most of these devices run some flavor of embedded Linux. When combined with the bandwidth required to stream video, they provide a potent class of DDoS bots,” continues the post.
According to the experts, crooks behind the botnets have used some of the C&C servers to launch more than 100 attacks per day.
“Most attacks are short-lived, with the median duration just over 2 minutes, and 75 percent of attacks shorter than 5 minutes.”
“The use of IoT devices in botnets is not new, but as they become more common, we expect these types of botnets to increase in number and power,” Level 3 said in a blog post. “The security of IoT devices poses a significant threat. Vendors of these devices must work to improve their security to combat this growing threat. ”
[adrotate banner=”9″]
(Security Affairs – BASHLITE malware, IoT)