
The German researcher Maxim Rupp has discovered numerous security issues in clean energy systems, including solar lighting and wind turbines. The possible consequence of a cyber attack is the interruption of energy supplies. According to the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT), the most disconcerting aspect related to the security vulnerabilities is the low level of skill necessary for their exploitation.
Rupp reported several security flaws in the web controls for the following systems:
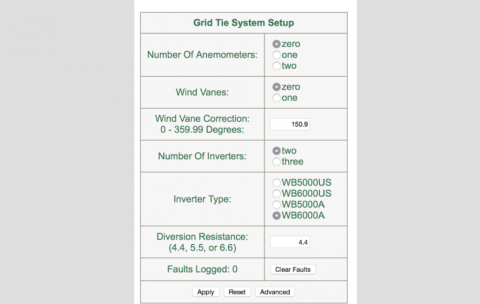
The cross-site request forgery vulnerability affecting the XZERES turbine could be exploited by hackers to change the administrator password for the web management interface. The attackers will gain complete control of the turbine, as explained by the researcher he would “change the wind vane correction, or change the network settings to access the web interface that would make it inaccessible. This can be certainly critical for the implementation of a successful attack.” The ICS-CERT ranked the security issue as 10 of 10 on the standard Common Vulnerability Scoring System, the organization considers dangerous the flaw due to the ease of remote exploitation.
Let’s now consider the flaw discovered by Rupp in the Sinapsi monitoring and management system of small size photovoltaic plants. As explained by the expert the flaw allows to view saved passwords going through the linked mail system, fortunately, the vulnerability is not exploitable remotely.
The vendors for the first two security issued have already provided a fix for the problems so the US government urges users to patch their systems as soon as feasible.
The third flaw discovered by Rupp in the RLE Nova-Wind Turbine. The expert noticed that the passwords to access the web interface are stored in a plaintext file.
“This could allow a malicious user to access the device and make changes to the configuration without authentication,” ICS-CERT noted.
Unfortunately the ICS-CERT tried several times to contact the German vendor RLE International without success.
“ICS-CERT has attempted on multiple occasions to contact the vendor regarding this serious flaw and have according to our vulnerability disclosure policy now produced this advisory,” the advisory read.
As explained by several times and reported in an interesting post published by Forbes on the subject, it is quite easy to locate and hack SCADA systems worldwide thanks the availability of the Shodan search engine.
“FORBES was able to find 31 Sinapsi-related systems, 18 XZERES 442SR servers and one Nova-Wind Turbine. Most of the Sinapsi lights were in use at an Italian university, the Universita di Napoli Federico II, so if any hacker wanted to cause a blackout at the world’s oldest state university, they have some potentially good entry points.” states Forbes.
“But using some of Rupp’s vulnerabilities, it would be possible for hackers sitting at their desk thousands of miles away to go further, to break into the systems and shut them down. This is not just theoretical. As the US ICS-CERT warns, anyone who can grab credentials for the Nova-Wind turbines, just by sitting on the wire and snooping on the traffic, can “gain unauthenticated access to the device. This means that a malicious party could perform any action on the device including change or modify configurations and settings.”” states Forbes
“At the moment In Europe there are a lot of wind turbines from different manufacturers which are available via the internet,” Ruppadded.
Unfortunately, the majority of SCADA systems is not designed to stay online, they lack security by design, for this reason, are exposed to remote exploitation that can cause serious consequences.
It’s time to control assess and improve the security of control systems worldwide, before it will be too late.
(Security Affairs – SCADA, hacking, wind turbines)