
Hundreds of banks and financial institutions across the world may have been infected with a sophisticated fileless malware that is hard to detect.
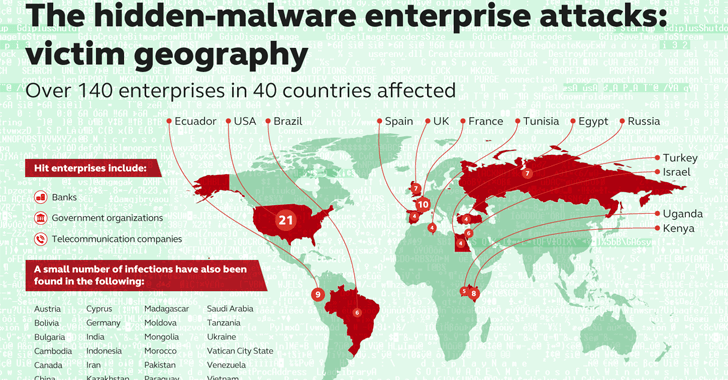
The threat was discovered by the experts at security firm Kaspersky Lab, the crooks are targeting organizations in many industries. Banks, telecommunication companies, and government in 40 countries were infected with a fileless malware that resides in the memory of the compromised computers and does not copy any files or folder to the hard drive.
The researchers discovered that the fileless malware already infected systems in 140 enterprise networks, with most victims located in the US, France, Ecuador, Kenya, the UK, and Russia.
Researchers believe that the real number of victims is likely much higher because the threat is very hard to detect.
Malicious code is directly injected into the memory of the infected machine and the malware executes in the system’s RAM.
“A good example of the implementation of such techniques is Duqu2. After dropping on the hard drive and starting its malicious MSI package it removes the package from the hard drive with file renaming and leaves part of itself in the memory with a payload. That’s why memory forensics is critical to the analysis of malware and its functions. Another important part of an attack are the tunnels that are going to be installed in the network by attackers.” reads the analysis published by Kaspersky.
The attack was first spotted by a bank’s security team that discovered a copy of the Meterpreter code, an in-memory component of the Metasploit framework, in a physical memory of a Microsoft domain controller (DC).
The experts at Kaspersky Lab tracked the threats as MEM:Trojan.Win32.Cometer and MEM:Trojan.Win32.Metasploit. The malware leverage PowerShell scripts within the Windows registry to load the Meterpreter code directly into memory, similar techniques leveraging on the PowerShell were already adopted by other malware in the wild.
“Kaspersky Lab participated in the forensic analysis after this attack was detected, discovering the use of PowerShell scripts within the Windows registry. Additionally it was discovered that the NETSH utility as used for tunnelling traffic from the victim’s host to the attacker´s C2.” continues the analysis.
Which is the motivation?
The hackers appear to be interested in compromising systems that control ATMs, but the investigation is still ongoing.
Kaspersky Lab researchers plan to reveal more details in April about the attack, which is occurring on an industrial scale worldwide.
[adrotate banner=”9″]
(Security Affairs – Fileless malware, cybercrime)