
McAfee researchers believe that the NetWalker ransomware operators continue to be very active, the gang is believed to have earned more than $25 million since March 2020.
The malware has been active at least since August 2019, over the months the NetWalker ransomware was made available through a ransomware-as-a-service (RaaS) model attracting criminal affiliates.
McAfee published a report about NetWalker’s operations, the researchers were able to track payments monitoring transactions to a pool of known Bitcoin addresses associated with the ransomware operators.
“Since 2019, NetWalker ransomware has reached a vast number of different targets, mostly based in western European countries and the US. Since the end of 2019, the NetWalker gang has indicated a preference for larger organisations rather than individuals.” reads the report. “During the COVID-19 pandemic, the adversaries behind NetWalker clearly stated that hospitals will not be targeted; whether they keep to their word remains to be seen.”
NetWalker ransomware operators have recently begun choosing affiliates specialized in targeted attacks against high-value entities in the attempt to maximize their effort with surgical operations.
High-value enterprises are expected to pay bigger ransom demands compared to small companies.
The affiliates used to deliver the threat via brute-forcing attacks on RDP servers or exploiting known vulnerabilities in VPN servers and firewalls.
The NetWalker author, who goes online with the moniker “Bugatti”, was only interested in doing business with Russian-speaking customers.
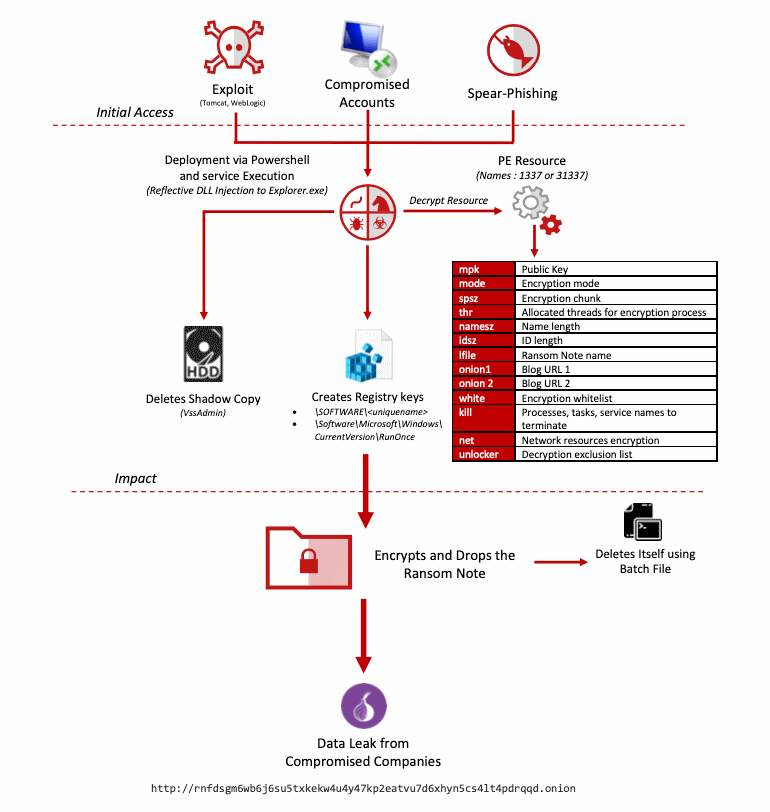
Threat actors spreading the NetWalker ransomware carried out cyber attacks that leveraged exploits in Oracle WebLogic and Apache Tomcat servers, brute-forcing RDP endpoints, and carrying out spear-phishing attacks on staff at major companies.
Last week, the FBI has issued a new security flash alert to warn of Netwalker ransomware attacks targeting U.S. and foreign government organizations. The feds are recommending victims, not to pay the ransom and reporting incidents to their local FBI field offices.
The flash alert also includes indicators of compromise for the Netwalker ransomware along with mitigations.
The FBI warns of a new wave of Netwalker ransomware attacks that began in June, the list of victims includes the UCSF School of Medicine and the Australian logistics giant Toll Group.
“As of June 2020, the FBI has received notifications of Netwalker ransomware attacks on U.S. and foreign government organizations, education entities, private companies, and health agencies by unidentified cyber actors.” reads the alert. “Netwalker became widely recognized in March 2020, after intrusions on an Australian transportation and logistics company and a U.S. public health organization. Cyber actors using Netwalker have since taken advantage of the COVID-19 pandemic to compromise an increasing number of unsuspecting victims.”
The Netwalker ransomware operators have been very active since March and also took advantage of the ongoing COVID-19 outbreak to target organizations.
The threat actors initially leveraged phishing emails delivering a Visual Basic Scripting (VBS) loader, but since April 2020, Netwalker ransomware operators began exploiting vulnerable Virtual Private Network (VPN) appliances, user interface components in web apps, or weak passwords of Remote Desktop Protocol connections to gain access to their victims’ networks.
Recently the Netwalker ransomware operators were looking for new collaborators that can provide them with access to large enterprise networks.
“Two of the most common vulnerabilities exploited by actors using Netwalker are Pulse Secure VPN (CVE-2019-11510) and Telerik UI (CVE-2019-18935).” continues the alert. “Once an actor has infiltrated a network with Netwalker, a combination of malicious programs may be executed to harvest administrator credentials, steal valuable data, and encrypt user files. In order to encrypt the user files on a victim network, the actors typically launch a malicious PowerShell script embedded with the Netwalker ransomware executable.”
The analysis of the transactions related bitcoin addresses involved in the Netwalker ransomware operations, McAfee observed 2,795 bitcoins being transferred between wallets operated by the gang between March 1st, 2020, and July 27th,2020.
“The total amount of extorted bitcoin that has been uncovered by tracing transactions to these NetWalker related addresses is 2795 BTC between 1 March 2020 and 27 July 2020. By using historic bitcoin to USD exchange rates, we estimate a total of 25 million USD was extorted with these NetWalker related transactions,” continues the McAfee’s report.
“Even though we do not have complete visibility into the BTC flow before NetWalker started ramping up, one thing is certain, this quarter alone it has been highly successful at extorting organisations for large amounts of money.”
In order to force the victims into paying the ransom, the gang set up a leak site where it publishes the data of the victim that refuse to pay. This tactic is becoming very common in the cybercrime ecosystem and many companies decided to pay to avoid having their name listed on the site and their data leaked online.
McAfee also shared YARA rules for the threat along with Indicators of Compromise and MITRE ATT&CK Techniques.
| [adrotate banner=”9″] | [adrotate banner=”12″] |
(SecurityAffairs – hacking, ransomware)
[adrotate banner=”5″]
[adrotate banner=”13″]